How to Achieve Customer Data Security & CCPA Compliance in Bloomreach
By Annabel Pemberton
02/08/2021
Bloomreach prides itself on having a full suite of security tools and new addition has recently joined our team.
Two years ago, the General Data Protection Regulation (GDPR) came into existence. For many, other than sending out emails to let customers know about the regulation, nothing really changed. Two years later, we are beginning to see how the law will respond and issue fines in response to non-compliance.
In mid-August, CCPA regulations received final approval and took immediate effect. This affects any company that targets residents of California. Whether it will follow the same trajectory as the GDPR will soon be seen. However, GDPR has shown us that being aware of the risk and how your data is being handled in your organization is less expensive than trying to weather the storm if a breach occurs.
Data protection also coexists with security, with both having the aim of keeping data safe. With more employees using devices from home, cybersecurity threats are on the rise, with a 400% increase in cyber attacks every day since the COVID-19 pandemic started.
Why Should You Care?
With names of various data protection regulations being overused, it is hard to distinguish what is truly important for your organization. For us, there are four main reasons it is important to take data protection seriously:
1. Bad Security Alarms Customers and Security is a Customer Priority
If there is one thing that has changed during the last few months, it is the use of video conferencing becoming a norm for communication. However, this change also was tied to customer concerns around the security of video conferencing platform Zoom. We only need to look at the amount of discussion around Zoom in April 2020 to see this. Therefore, despite GDPR’s initial slow takeoff, it has been shown that security and privacy are reasons for a consumer to change the tool they are using.
2. Solving a Security Breach Rather than Taking Preventative Measures is More Expensive and Wastes Time.
Prevention is always better than a cure.
This applies also to security and GDPR/CCPA, and can be shown with how resource-intensive data leaks can become if they are poorly managed. Taking care of a breach after it happens has been shown to cost 1.2 million in damages. August 2020 reported 36.6 million records breached, making it the third-highest month for data breaches. It is therefore imperative that your organization is prepared to protect your assets and time later down the line.
3. A Breach is Not Cheap…
Even if you believe it would be better to wait for the storm and try to pay your way out, as fine sizes increase, this would not be an optimal strategy.
So how expensive is expensive?
According to IBM, the average cost of a data breach in the US is 8.2 million dollars, which is the highest total average cost of any country. This includes the labor-intensive cost that goes behind resolving the incident, with it taking globally 279 days on average to identify and contain a breach.
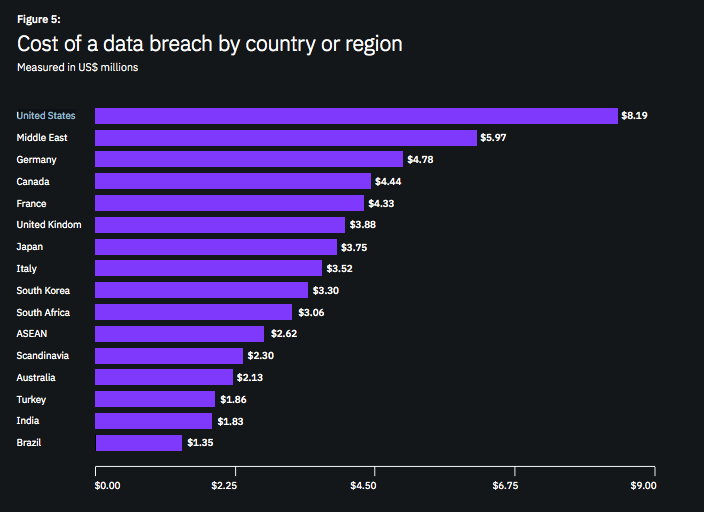 Source: IBM
Source: IBM
4. Many Companies are Now Facing Breaches
More than ever, companies are facing vulnerabilities in their system and witnessing vulnerabilities being utilized. This heightened occurrence has also been in parallel with the introduction of privacy regulations, which pose extra scrutiny on these companies.
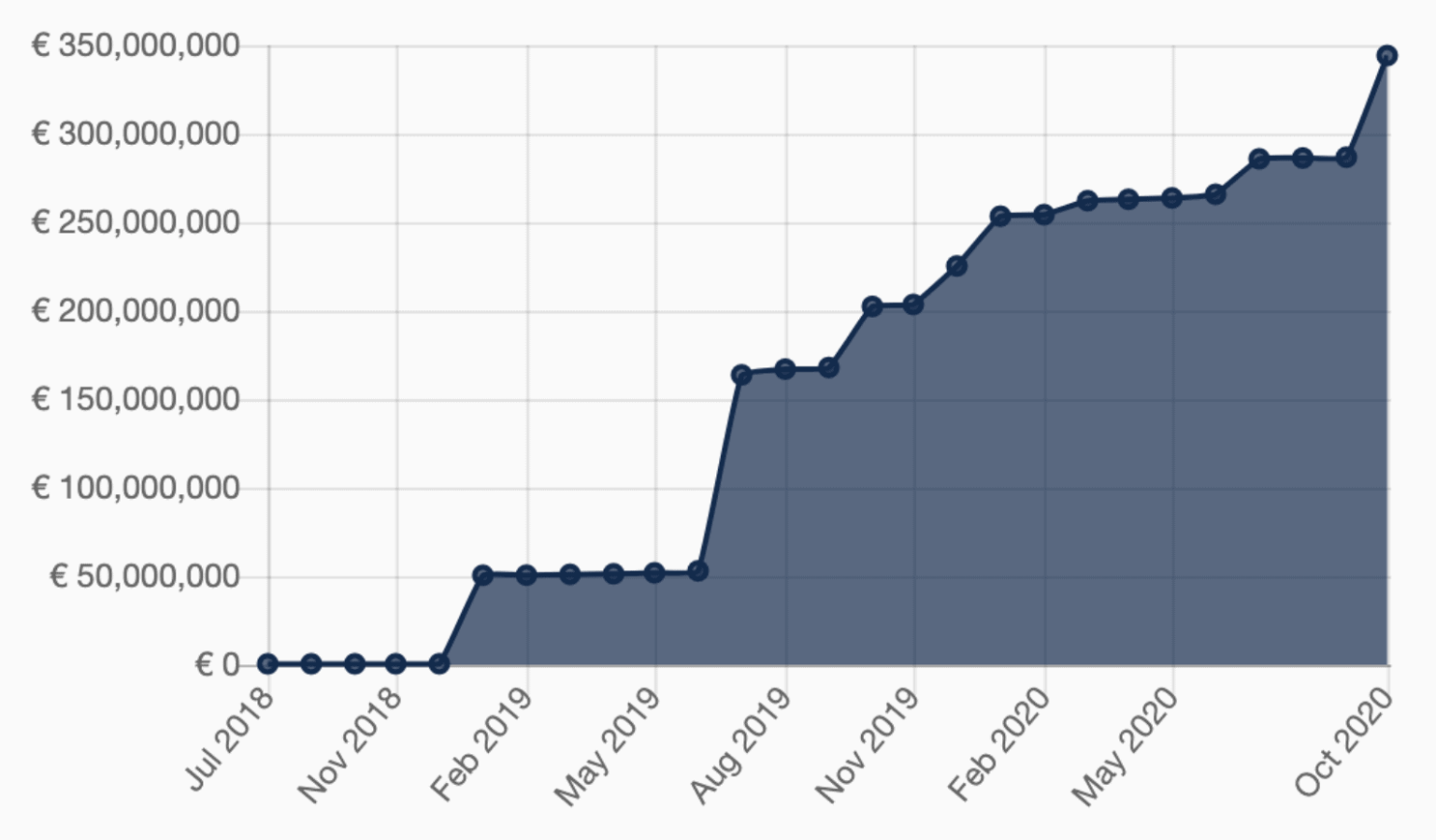 Source: Enfourcement Tracker
Source: Enfourcement Tracker
This also isn’t just about GDPR fines. In May 2020 alone, there were 8.8 billion data records breached.
The Risks in Not Addressing Security
In addition to the reasons above, failing to address security can also lead to a loss in customer trust and reputational damage.
However, this is only a risk if you are not secure or complaint with data protection regulations.
So What Does it Mean to be Secure and CCPA Compliant?
While security relates to the technicalities and regulations relate to the legalities, both requirements seek to ensure the correct handling and usage of data. Therefore ensuring you can manage your data appropriately can ensure sufficient security and compliance.
For example, making sure only authorized members of your team are accessing your assets mitigates the risk of any suspicious or unwanted people getting access.
But being Secure and Compliant is Expensive, Time Consuming and will Restrict My Creativity, Right?
This is one of the common pitfalls many companies fall into – seeing compliance and security in a dichotomous way. This fails to appreciate that they are both on a sliding scale determined by your organization. Of course, you need to meet some requirements in order to be compliant, but this doesn’t necessarily mean the work needs to be time consuming, costly or impersonal.
This is exactly the assumption we break down in our Bloomreach GDPR Academy, where you can learn about data protection and how to appropriately use Bloomreach in correlation with it.
To help you get on the right track we have also created a dedicated Security and Privacy package. SmartSafe is a package of services designed to acquaint your team to Bloomreach’s Security and data protection features. With SmartSafe you could:
- gain confidence on exactly how you are using your project
- reassure your Security and Data Protection team
- flex with changing regulations
- be prepared for outsider observation and audit
- turn fear to flexibility
One element of the package is a monthly Security and Compliance report.
These Reports are a Monthly Review of Your Project, Ensuring the Current Project Circumstances are Still Appropriate.
While Bloomreach has a suite of security features, how well these tools protect you depend on your usage in the project. We have created a service to maintain your control over your data, while giving you the reassurance that it is protected as we envisaged it to be.
The report is designed to continue to assess the security of your Bloomreach project, helping you to keep pace with the current data protection guidelines, security vulnerabilities and bad usage patterns. The report also gives explanations of the suggested solution and improvements to mitigate the risk, so you can be sure you know what to do to avoid harm.
The monthly report covers elements such as:
- Authorization settings
- Logs of activity of accessing PII
- Activity of users in the instance
- Usage of data protection features
Following the recommendations in the report is one way to help achieve compliance and security for your Bloomreach project, but it’s not the only way to get help.
You can see a full overview of all of Bloomreach’s security features in our dedicated e-book, Bloomreach Security Features. This e-book takes a comprehensive look at how Bloomreach keeps your data secure, but uses easy-to-understand terms to do so.
Found this useful? Subscribe to our newsletter or share it.